Updated at 07/09/2023 - 04:10 pm
There is a major change in the process and approach to tax audits and tax administration
Trends in changes related to the tax examination and analysis process
The way that businesses need to approach appropriately and change their thinking in the matter of tax obligations
In the past, the tax inspection process often focused on checking each item individually, sometimes causing inconvenience to businesses and time consuming. But now, the Tax Authority has switched to using information technology to manage tax data and invoices synchronously, creating favorable conditions for analysis, assessment and risk classification for businesses. .
Below are the major changes in the process and approach to tax audits and tax administration
1. Build a centralized taxpayer database #

i) Building a centralized taxpayer database
Information technology helps to synthesize and manage tax and invoice data accurately and efficiently, thereby creating a clear view of the financial position of the business.
- Tax authorities develop a database of taxpayers that is built and managed centrally at the General Department of Taxation
- Deploying a centralized electronic invoice management and database system at the General Department of Taxation
ii) Building data analysis tools based on information technology (AI)
By using technology to analyze data, Tax Offices can create early indications of potential tax and financial problems, the following tools are in place:
- The application supports the whole test to evaluate and select high-risk taxpayers. See the detailed article of Decision 970/QD-TCT on Tax Inspection Process (Effective from 14/07/2023) and The application supports the whole test
- Electronic invoice data analysis system in order to evaluate and identify enterprises showing signs of risks in the management and use of invoices. See detailed article Deployment of database analysis and e-invoice management system
2. Data communication and data collection outside the tax authority #
The sources and methods of collecting information on tax obligations are applied as follows:
i) Information collection in tax authorities
Including information within the scope of collection and management of tax authorities, that is: Tax registration information; information on the identities of the founding members, owners and legal representatives of taxpayers; Information about affiliate transactions…
ii) Collect taxpayer information from agencies other than tax authorities
Information collected from relevant state management agencies, organizations and individuals responsible for providing, including:
- Information about taxpayers from the bank; Card-looking Things to know about providing banking transaction data to tax authorities
- Information about Labor; Social insurance. View Post Data sharing between Social Insurance (SI) and Tax Authority
- Information from relevant ministries and agencies and Information from foreign countries and international organizations.
3. Analyze, evaluate and audit taxes based on tax risk classification #
i) Analysis – evaluation
The Tax Office can identify businesses that are more at risk and focus their checks on the most important issues.
The assessment and supervision activities of tax authorities include:
- Collect, process, manage and use information related to taxpayers for risk management.
- Assess tax compliance and classify taxpayers' risk.
- Apply tax management professional measures corresponding to the level of tax compliance and taxpayer risk.
- Regulations on criteria, indicators of compliance assessment criteria and risk classification of taxpayers as businesses and individuals.
The principles of management and control are as follows:
The tax authority shall base itself on the results of the assessment of compliance with the above-mentioned tax laws and professional information at the time of decision-making to determine a list of taxpayers classified by risk levels in each period.
The list of taxpayers at risk according to the above cases is updated on the risk management application in tax management.
i) High risk: Review, check, verify; Inspection, testing
ii) Medium risk: Randomly selected to be included in the list of review, check and verify; Continue to perform risk classification for the next assessment period
iii) Low Risk: Save records, perform risk classification for the next audit period.
In case of high compliance: Include in the list to consider, choose to commend and reward taxpayers who comply with tax laws.
See detailed instructions Tax risk assessment and key monitoring of taxpayers applied from July 02, 07
ii) Tax audit based on risk rating
In order to quickly check for at-risk taxpayers, tax authorities apply "The application supports the whole test" with the following procedure:
Step 1: Check tax records: No later than 25 days after the deadline for filing tax returns, tax officials assigned to tax audits shall use test application software to check and make a list of high-risk taxpayers.
Step 2: Processing test results and notifications: For tax records that are assessed as having a high total risk score, a list will be generated on the application to perform an inspection at the tax office. At the same time, the results from this inspection step will be combined with the inspection plan and the inspection plan at the tax office.
As such, this process helps tax authorities focus on quickly checking taxpayers who are at high risk for tax compliance through the use of the Full Check Support App. This enhances the ability to manage and handle potential tax violations.
4. Monitor sales transactions closely through the electronic invoice system #

i) Electronic invoice analysis and management system:
The General Department of Taxation deploys a system to analyze and manage electronic invoices of taxpayers.
This system will be able to compare electronic invoice data with tax declarations, evaluate invoice usage, localize doubts and warn of risks.
See detailed article Deployment of database analysis and e-invoice management system
ii) Apply K factor to check invoices that exceed the safety threshold
On June 14, 6, the General Department of Taxation issued Official Dispatch 2392_TCT_QLRR dated June 14, 6 on checking electronic invoices, thereby proactively checking taxpayers who issue invoices that exceed the safety threshold.
In particular, the General Department of Taxation stated that it has built functions on the electronic invoice application to meet the requirements of controlling electronic invoices and preventing the issue of false invoices. Some main functions are as follows:
– The system automatically controls the total value of goods sold on issued invoices compared to the threshold value of input goods calculated as K times the total value of inventory and total value of purchased goods. .
– The warning system operates according to parameter K.
How to calculate K coefficient
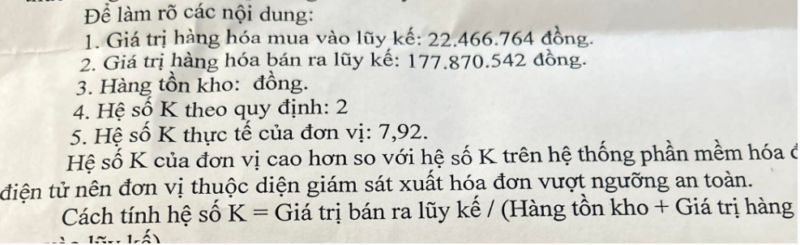
Based on Official Dispatch 2392/TCT-QLRR in 2023, the K coefficient is used to control the total value of goods sold on issued invoices compared to the threshold value of input goods calculated by the following formula:
K = Total value of goods sold on invoice / (Total value of Inventory + Total value of purchased goods on invoice)
Accordingly, when an enterprise exceeds the threshold value of input goods calculated as K times the total value of inventory and the total value of purchased goods, the system will issue an invoice warning and put it on the list. manage.
Some examples of explanation requirements due to exceeding the threshold according to the K coefficient
Below are some explanation requirements due to exceeding the K coefficient threshold

Disadvantages of K coefficient:
Because the K coefficient is calculated using mathematical logic without considering other conditional factors, mechanical manipulation of this coefficient may cause inspection warnings but there is no actual risk. For example, some types of processing businesses with revenue many times higher than the value of inventory + inputs fall into the risk list even under normal business conditions.
5. What do businesses need to do to avoid tax risks? #
We can draw an important point: Businesses need to manage their finances, accounting and tax declaration process strictly and comply with the law. The goal is to ensure that your business is on these lists businesses “do well” instead of having to deal with lying in list of “violations”
To make this happen, here are some important tips for both businesses and individuals:
- Understand the law: Master the regulations and guidelines related to data provision, tax return and tax payment. Make sure you understand how it's done and the restrictions and legal obligations you need to follow.
- Data systematization: Build and maintain a reliable tax, transaction and financial management system. This makes it easy for you to retrieve the necessary information when required by the tax authorities.
- Watch closely: Make sure you have correctly recorded the financial information. Check regularly to ensure accuracy of data.
- Getting ready for inspection and inspection: Make sure you have the necessary data and information ready to face any examination or inspection from the tax authorities.
- Keep relevant documents: Store all tax and financial related documents and vouchers for the specified time. This will help you demonstrate the accuracy and compliance of your information where necessary.
- Partnering with a financial and tax professional: Work with an experienced tax and finance professional or consulting firm to ensure you follow the right process and comply with the law.
Remember, complying with regulations and following the right processes not only helps you avoid legal risks, but also contributes to the transparency and financial health of your business.
Doing the above is not easy for businesses, the effective solution is to use a professional service: Cooperate with a financial, accounting and tax expert to ensure you follow the correct process and comply with the regulations. legislation.
See detailed information about our services in the article



